Vulnerability Details Report - Site
The Vulnerability Details Report - Site includes detailed descriptions of the vulnerabilities found in each site selected for the report, grouped by category. For reference purposes, the report includes relevant vulnerability details along with remediation instructions, followed by a list of specific instances of each vulnerability. This report helps developers effectively remediate vulnerabilities by providing an in-depth understanding of the findings for a particular asset.
Asset List
The Vulnerability Details Report provides a list of assets included in the report, shown below.
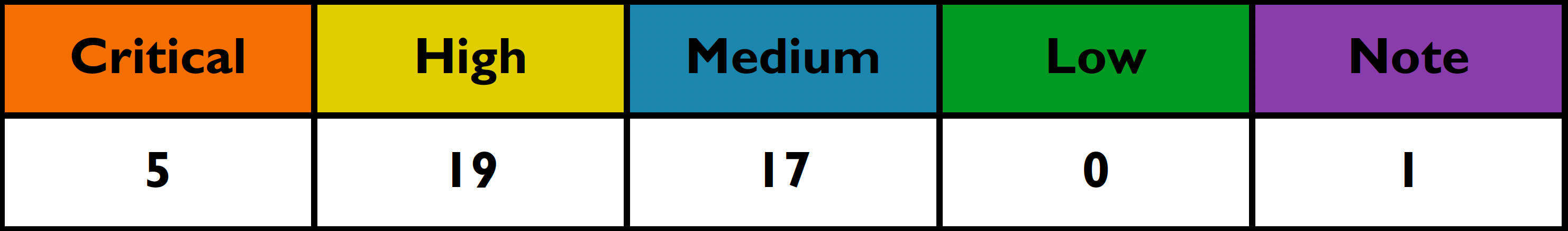
Summary Table
The summary table sorts by the importance (score) of your site set by the vulnerability assessor. The higher the score, the more important the site. Your vulnerabilities are then categorized by the vulnerability class and then by the vulnerability level.
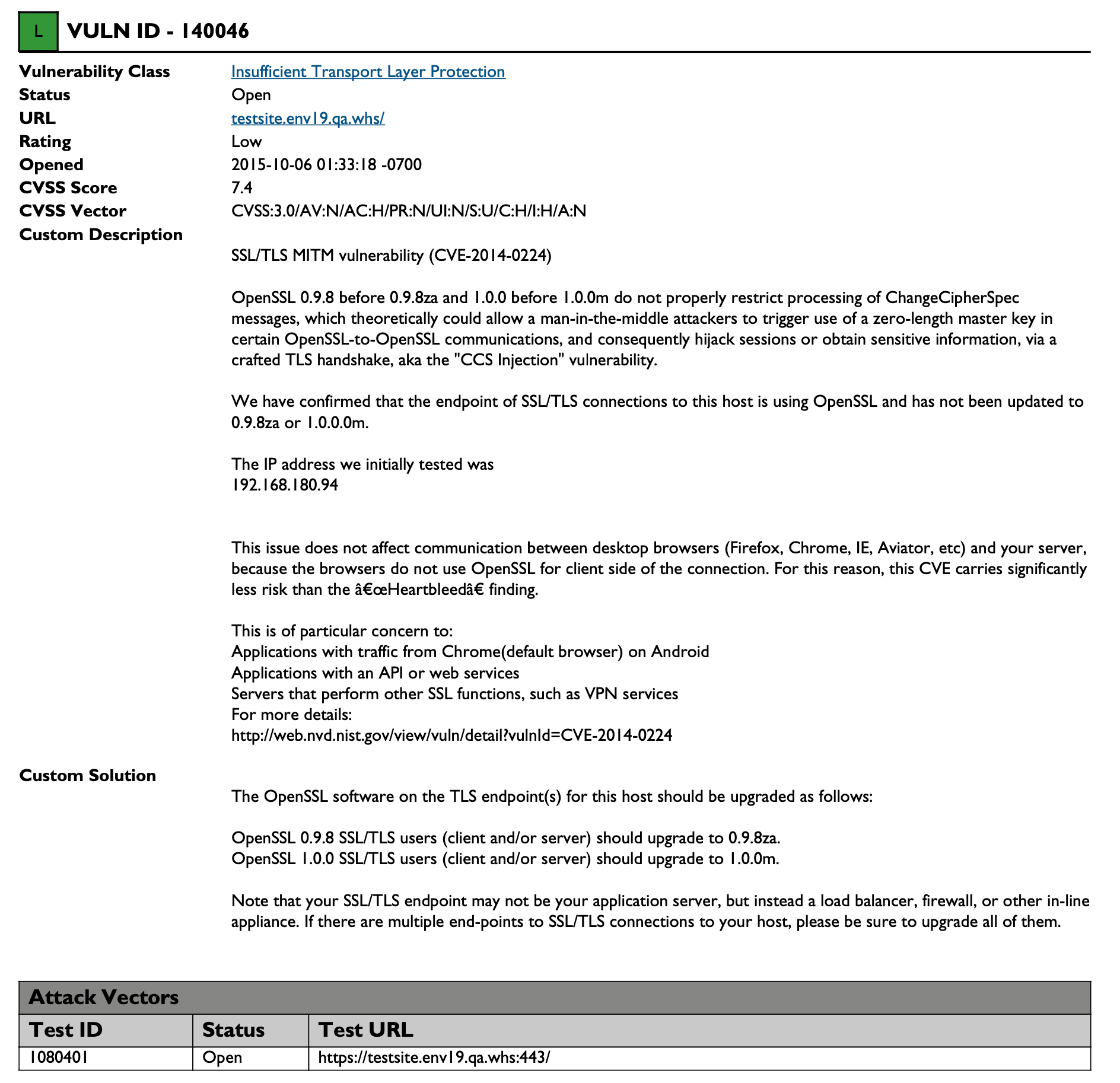
Individual Vulnerabilities
A sample report for Insufficient Transport Layer Protection is shown below; each vulnerability is reported in the same format.
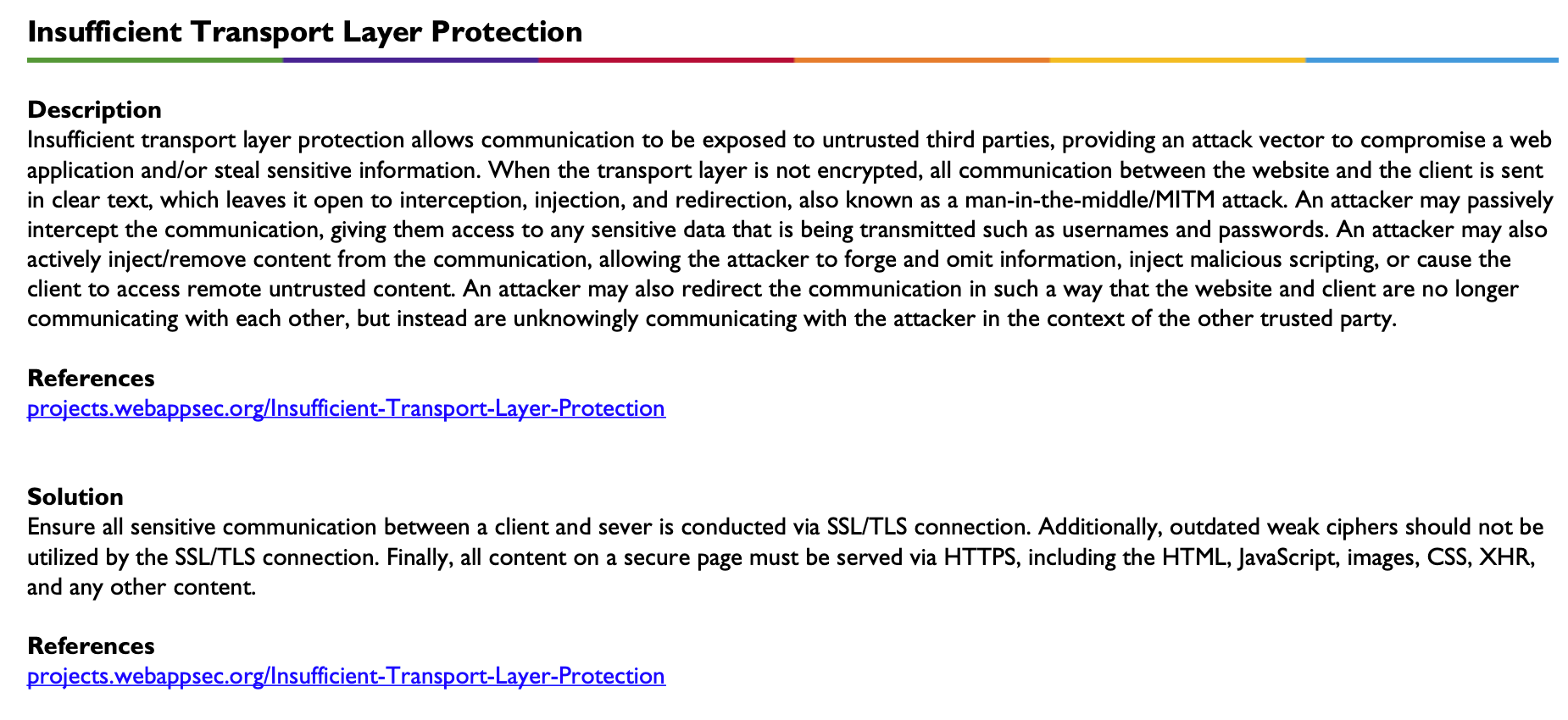
Definition
Descriptions and Solutions for each vulnerability class detailed in the table above are included in the report. References are provided for both description and solutions. A sample definition for Insufficient Transport Layer Protection is shown below.
Appendix - Vulnerability Level Definitions (by Risk)
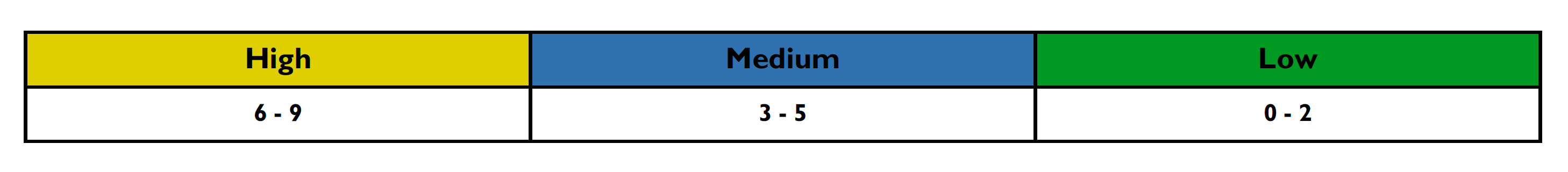
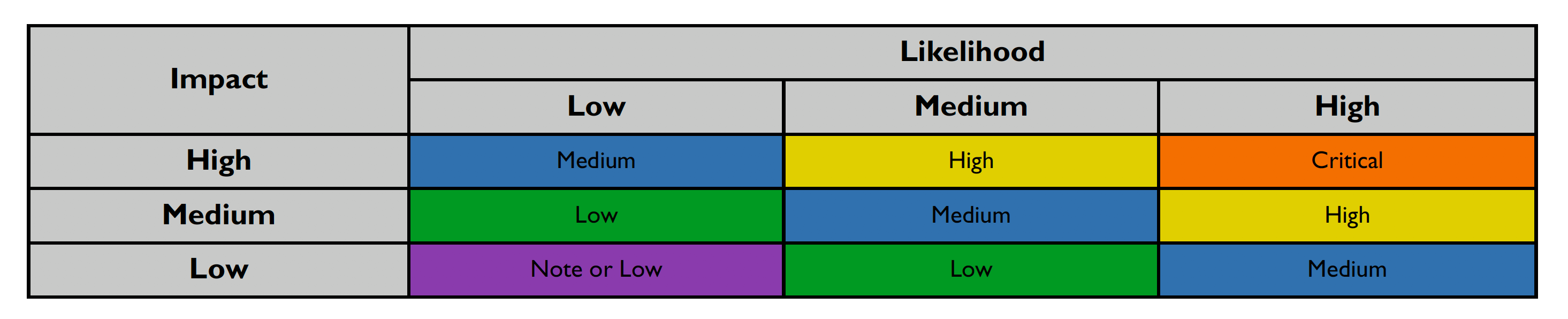
This section details how vulnerability levels are defined. Risk levels are based on the OWASP risk rating methodology and the standard risk model (Risk = Likelihood x Impact), with several factors contributing to likelihood and impact. The following tables show how vulnerability ratings are calculated in The Vulnerability Details Report.
-
The Impact can be broken down into the Technical Impact and Business Impact. Technical impact considers the traditional areas of security: confidentiality, integrity, availability, and accountability.
-
The business impact stems from the technical impact and considers things such as: financial damage, reputational damage, non-compliance, and privacy violations.
After scoring the Likelihood and Impact, the Risk Rating is determined using the following table:
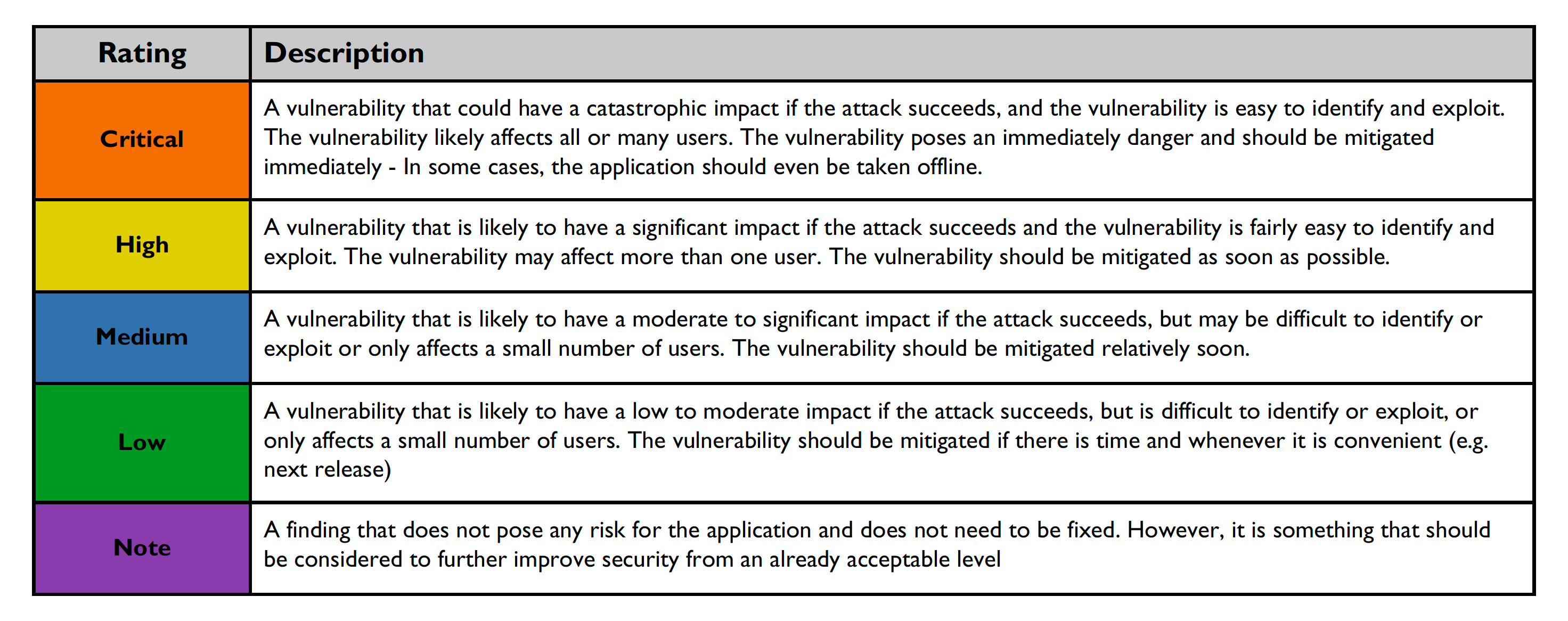
Risk ratings are defined below:
Vulnerability verification status indicated below:
The Vulnerability Details Report Options
The Vulnerability Details Report can be run for sites or groups; select your preference under the Generate For column in the Reports tab. You can select specific assets and specify:
-
Whether you want to see Open, Closed, or Both (all) vulnerabilities.
-
Which vulnerability classes you want to include in the detail report.
-
The date range for the report.
-
Which severity levels should be included in the report.
-
Whether or not Attack Vectors should be shown.
-
Whether or not the CVSS Score should be shown.
You can select what is to be included in the report by individual site or by group.
For more information on generating reports, please see Reports Section.