The Executive Summary Report
The Executive Summary Report shows you a summary of vulnerabilities by assets or by groups and by vulnerability class, as well as showing your overall security profile. For those customers using both Continuous Dynamic and Sentinel Source, this report will cover both dynamic and static test results. The Executive Summary Report displays a summary of the open vulnerabilities in four sections.
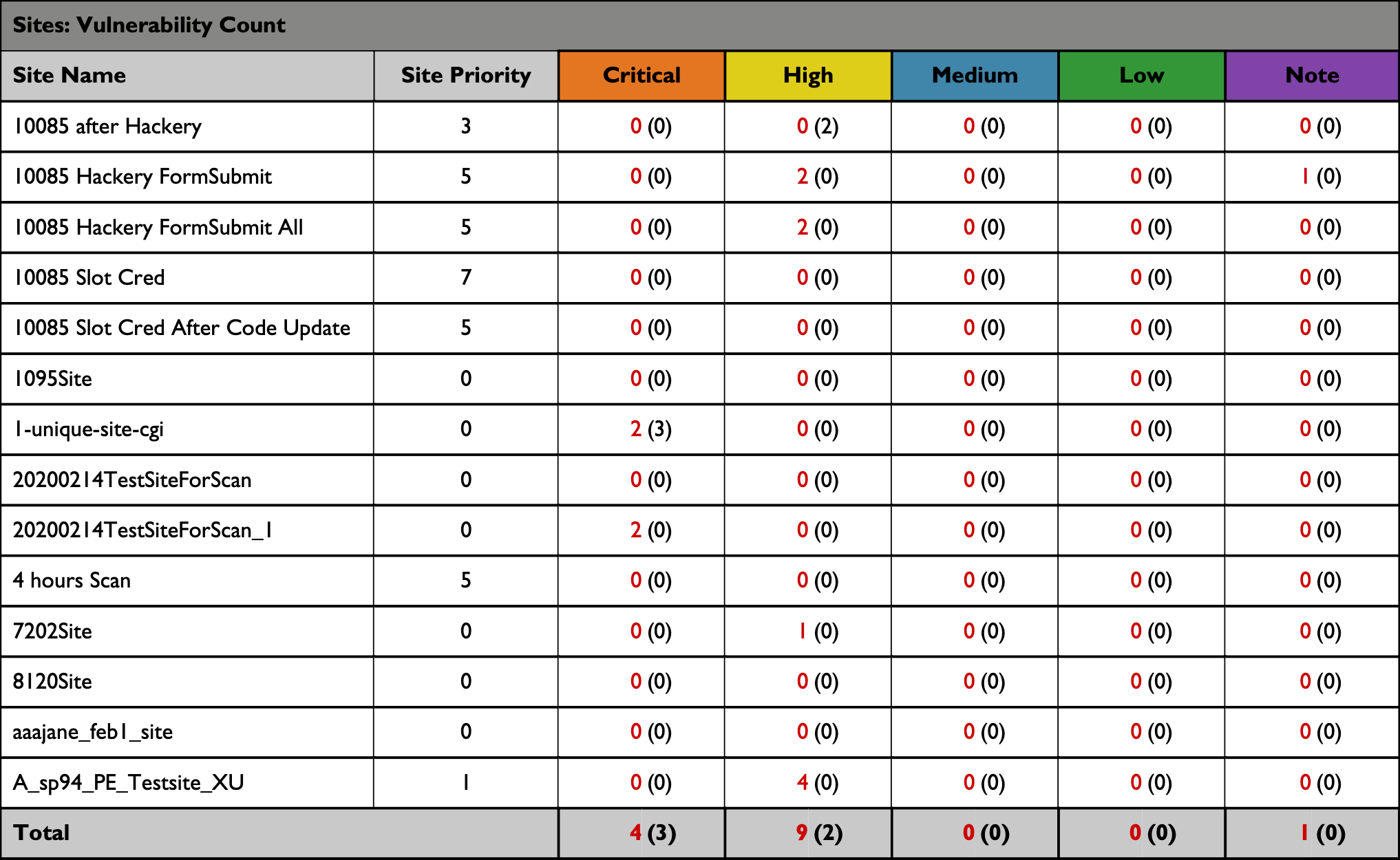
Vulnerability Count
The following table shows the number of vulnerabilities for each site, broken down by rating type.
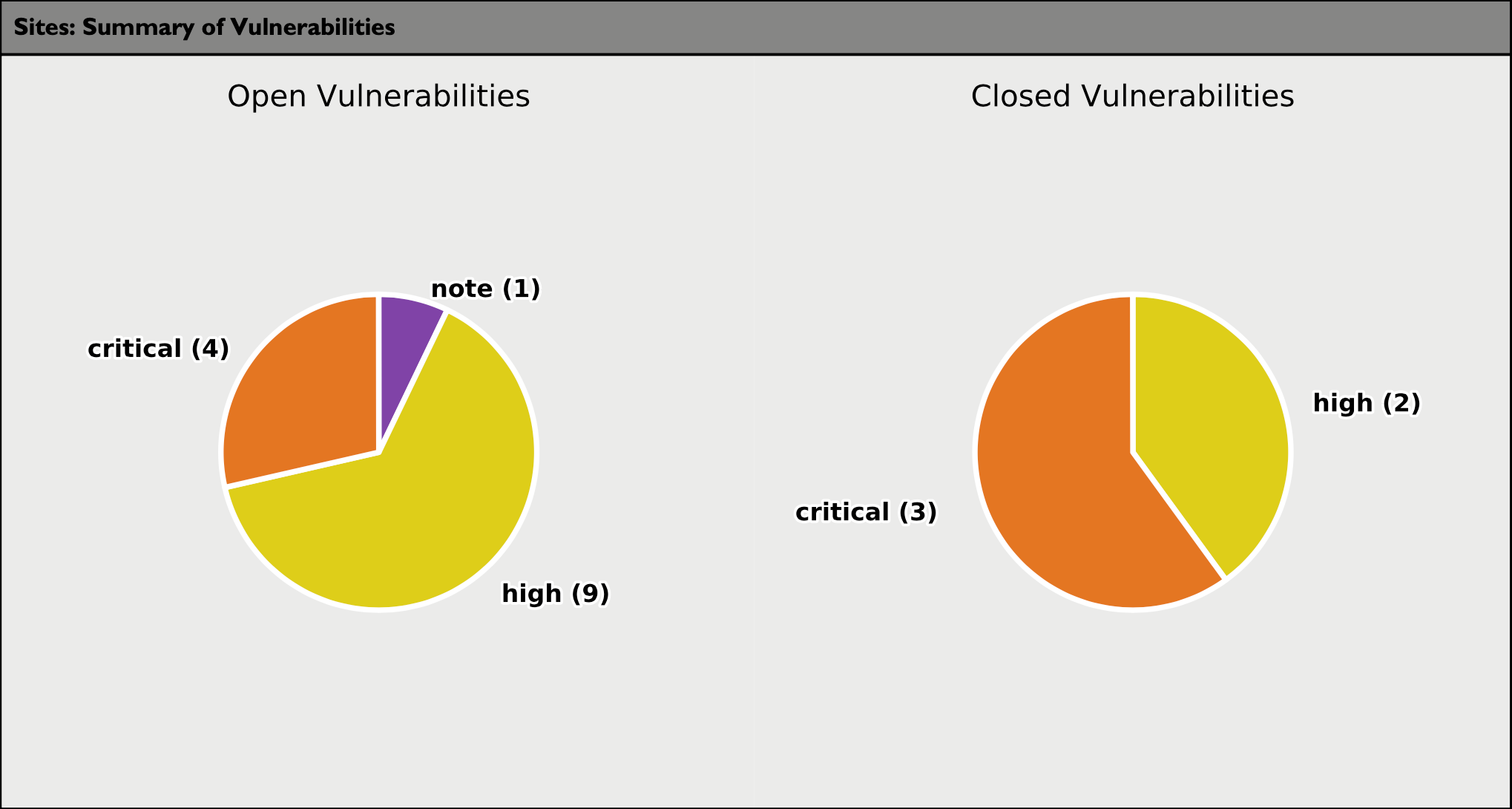
Summary of Vulnerabilities
The following pie chart summarizes the open and closed vulnerabilities and includes the vulnerability count.
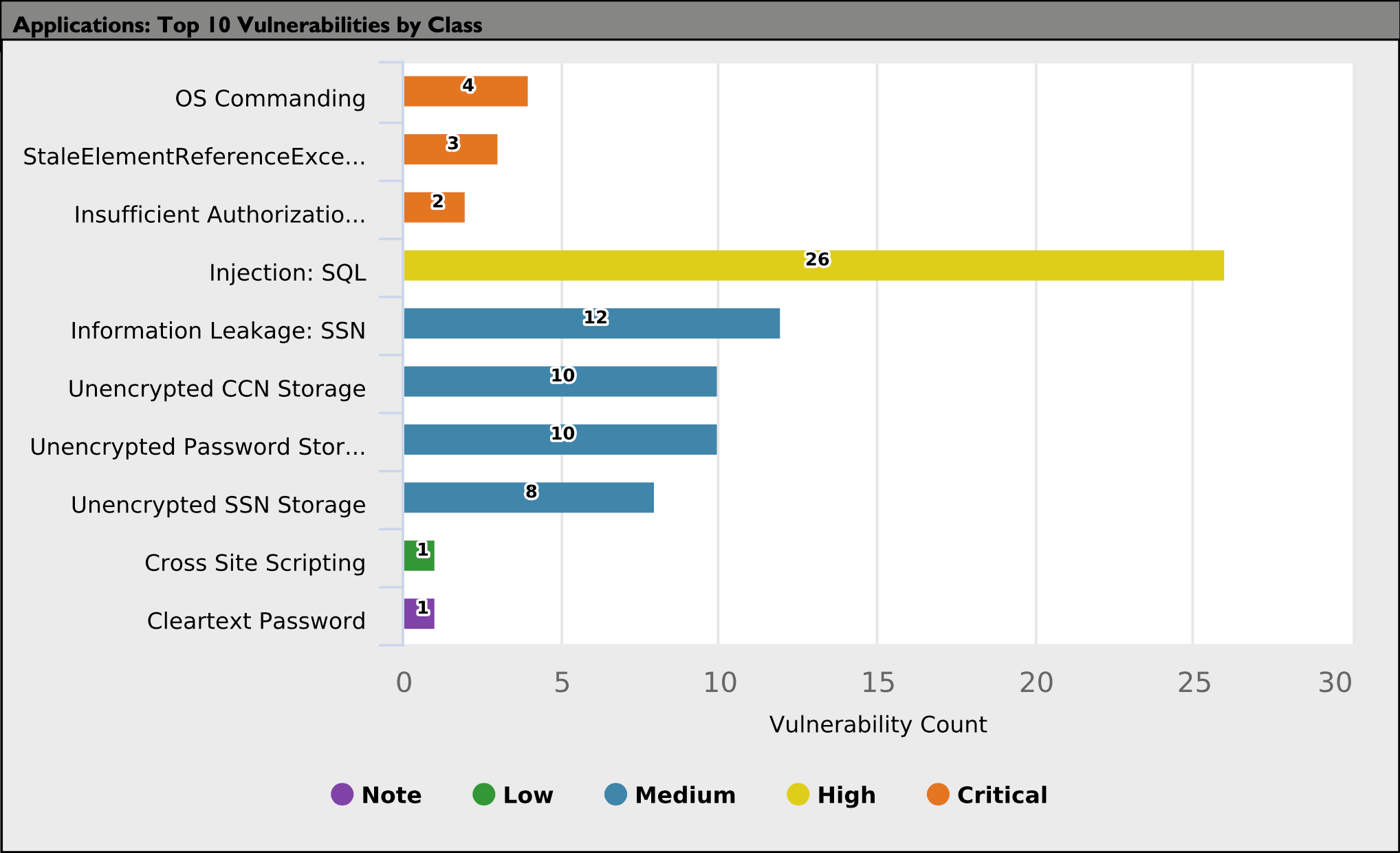
Top 10 Vulnerabilities by Class
The following graph displays the top 10 open vulnerabilities by class and includes the vulnerability count for each class.
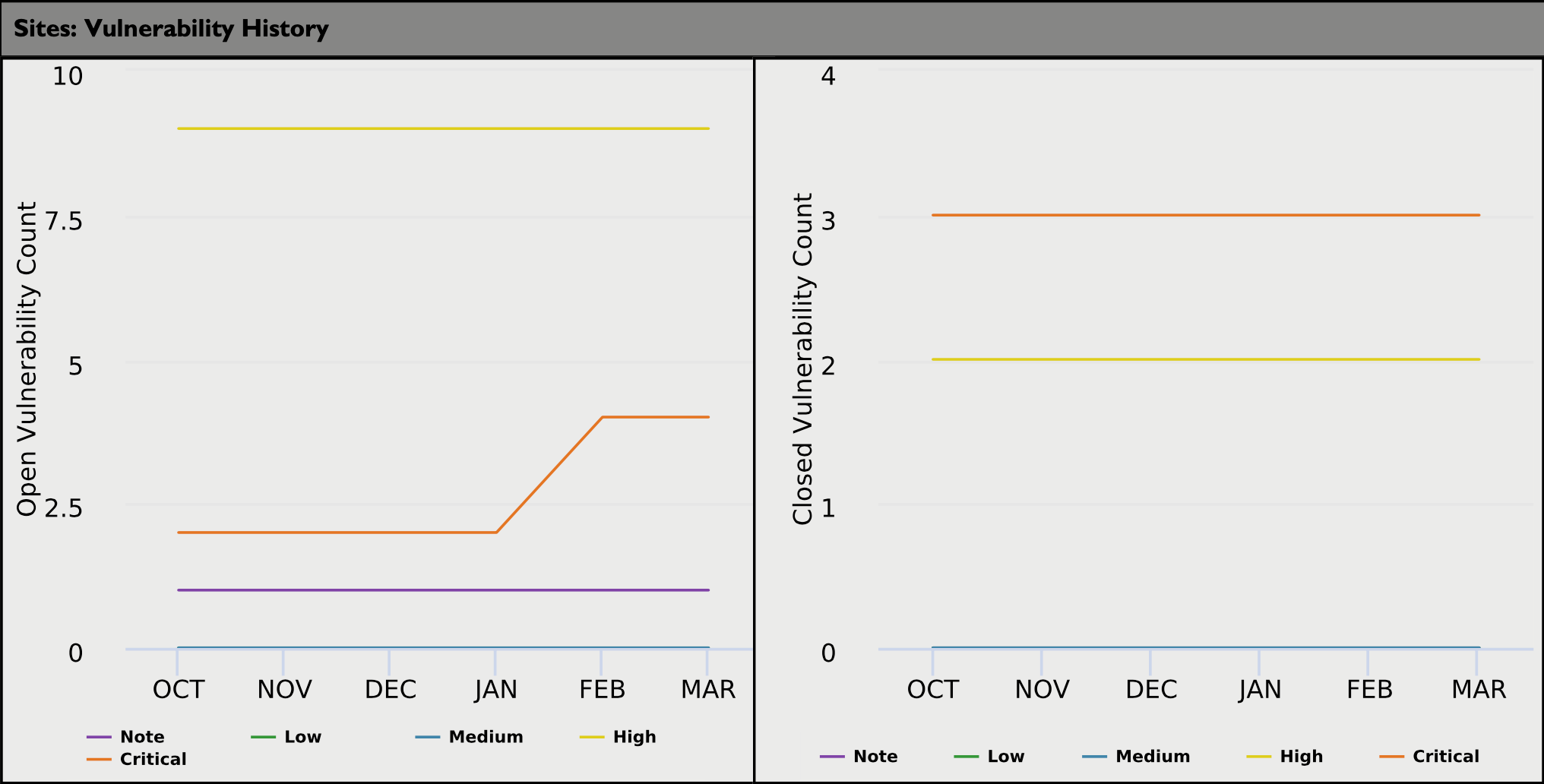
Vulnerability History
The following graph displays the vulnerability history and includes the vulnerability count for each class monthly.
| Data is compiled from the first of each month and is not a live data representation at time of report generation. |
Appendix - Vulnerability Level Definitions (by Risk)
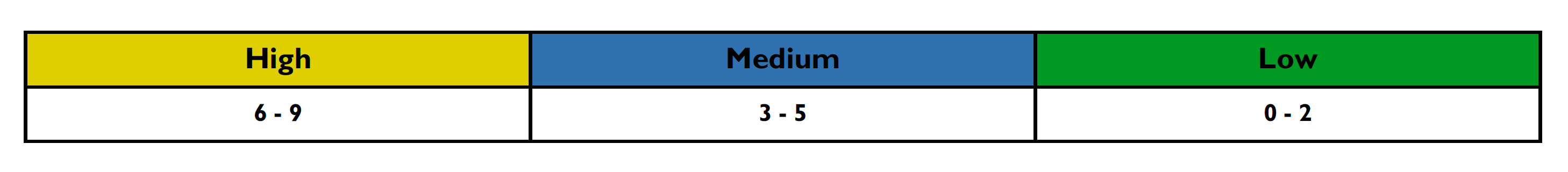
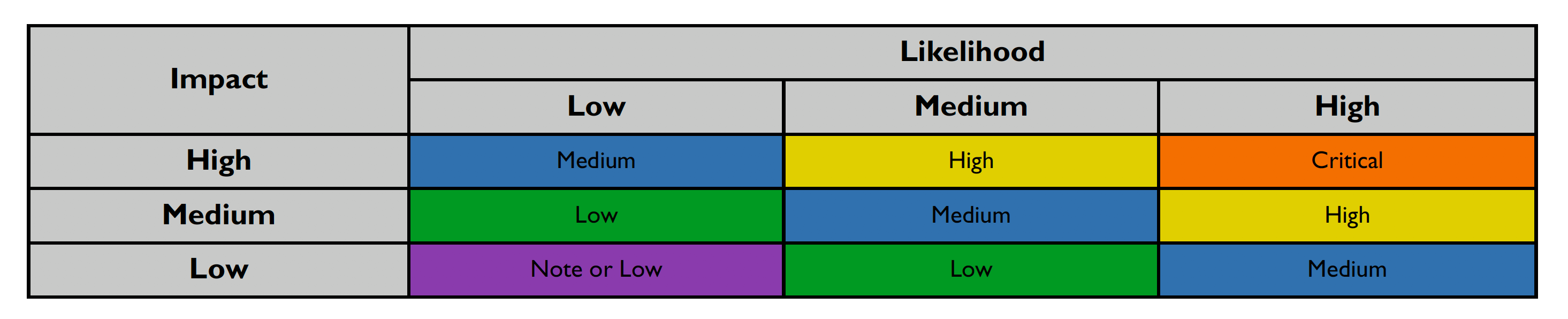
This section details how the vulnerability levels are defined, risk Levels for the Sentinel Source solution are based on the OWASP risk rating methodology, based on the standard risk model (Risk = Likelihood x Impact) with several factors contributing to the likelihood and impact. The following tables show how the vulnerability ratings are calculated in The Executive Summary Report.
-
The Impact can be broken down into the Technical Impact and Business Impact.
-
Technical impact considers the traditional areas of security: confidentiality, integrity, availability, and accountability.
-
The business impact stems from the technical impact and consider things such as: financial damage, reputational damage, non-compliance, and privacy violations.
-
After scoring the Likelihood and Impact, the Risk Rating is determined using the following table:
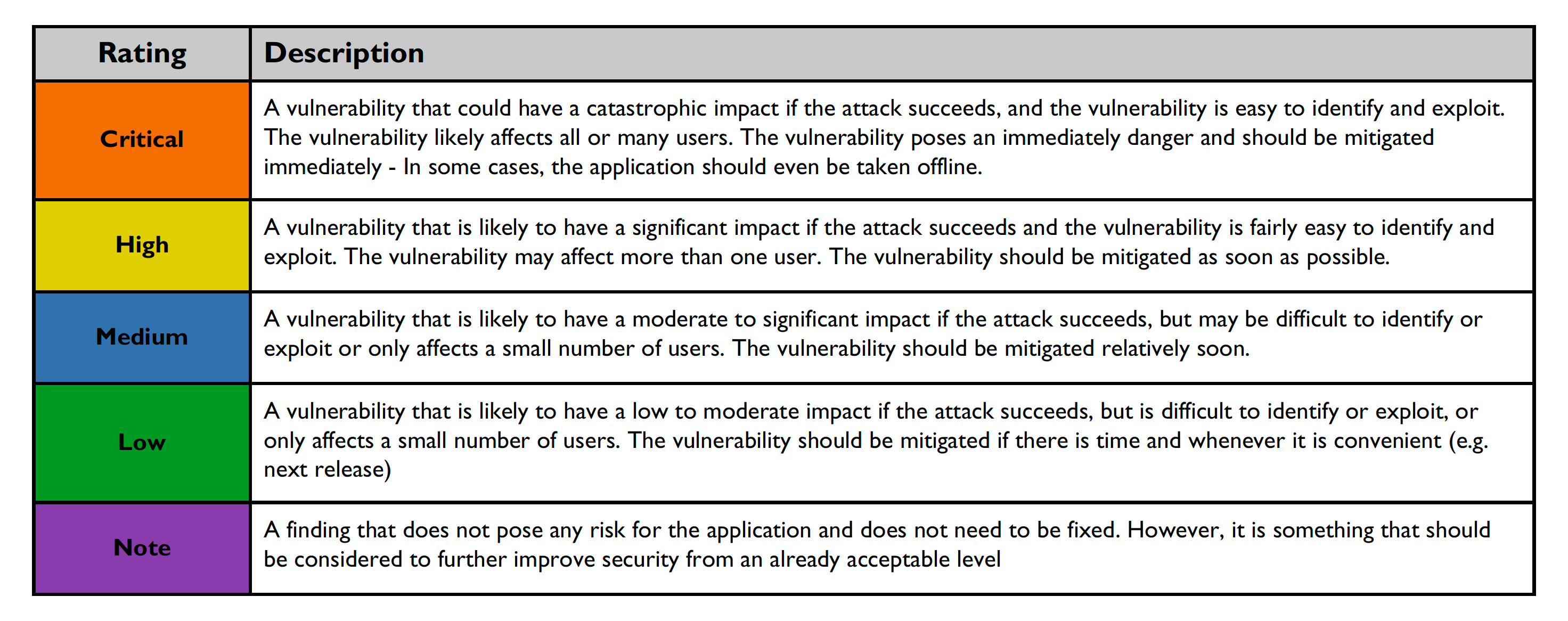
Risk ratings are defined below:
The Executive Summary Report Options
The Executive Summary Report can be run for Assets or Groups; select your preference under Generate For in the Reports tab. This report can be filtered by vulnerability status — you can select all open vulns, all closed vulns, or both open and closed vulns. For more information on generating reports, please see Report Section